Why Cyber Risk Is an Existential Threat for Small and Medium-Sized Business
When a cyber attack hits, most organisations face the same grim reality: hours - if not days - of investigation, uncertainty, and operational disruption. Systems are scrutinised, compromised servers are analysed, and teams wait for forensic clearance before they can even begin to restore normal service.
YUDU Sentinel takes a fundamentally different approach - and it starts with architecture.
Containment by Design
At the core of YUDU Sentinel’s platform is a single-tenant model. Each client operates within its own fully isolated infrastructure, with no shared environment between organisations.
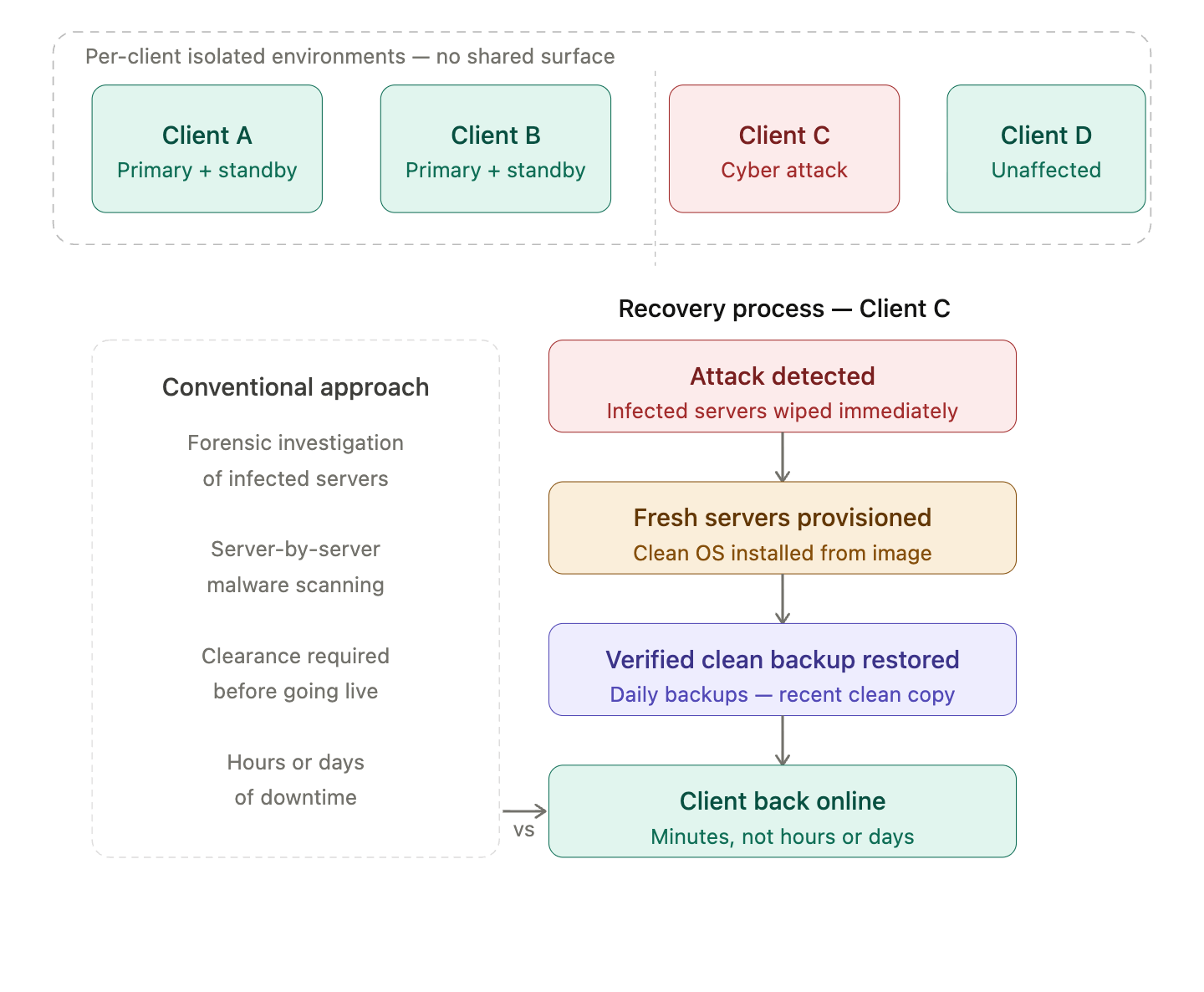
This means that if one client is attacked, the impact is completely contained. There is no lateral movement, no shared surface, and no risk of cross-client contamination. While many platforms rely on logical separation, Sentinel enforces physical and architectural isolation.
In practical terms: one client’s incident is never another client’s problem.
Recovery Without Delay
Where Sentinel truly diverges from conventional platforms is in how it handles recovery within a compromised environment.
The traditional approach is forensic-led. Teams investigate affected servers, attempt to understand the scope of the breach, and only then begin restoration. This process is slow, resource-intensive, and often uncertain.
The YUDU Sentinel approach removes that bottleneck entirely.
Instead of analysing compromised systems, it replaces them.
Infected servers are wiped. New servers are provisioned from clean, trusted images. A verified clean database backup is restored. The entire environment is brought back online in minutes - not days.
There is no waiting for forensic approval. No ambiguity about lingering malware. Just a clean, rapid reset.
The Architecture Behind the Speed
This recovery model is made possible by three key design principles:
- Redundant server architecture ensures high availability under normal conditions and supports rapid failover when needed
- Daily verified backups guarantee a recent, clean restore point is always available
- Single-tenant isolation ensures that backups are client-specific and untouched by any external compromise
Together, these elements eliminate the uncertainty that typically slows recovery efforts.
From Hours to Minutes: A New Recovery Standard
Most platforms define their recovery time objective (RTO) in hours or days following a serious incident. Sentinel fundamentally changes that equation.
Because it doesn’t rely on forensic investigation before recovery, its RTO is measured in minutes. It’s not just an improvement - it’s a shift in category.
This distinction matters most in high-pressure scenarios, where downtime directly impacts an organisation’s ability to respond, communicate, and operate.
Why It Matters to Different Stakeholders
YUDU Sentinel’s approach resonates differently depending on your role:
- For CISOs and security architects: eliminating the need for forensic investigation reduces cost, complexity, and recovery delays. It allows teams to focus on response, not analysis bottlenecks.
- For CFOs and risk owners: the value is clear in RTO. Faster recovery means reduced financial exposure, lower operational disruption, and greater business continuity.
- For critical national infrastructure (CNI) and government clients: the isolation model is key. Attacks cannot propagate between clients—not as a configuration choice, but as a built-in architectural guarantee.
Built for the Worst-Case Scenario
Many platforms are designed to be resilient under normal conditions. YUDU Sentinel goes further - it is designed to recover rapidly from the worst-case scenario.
For organisations that rely on their systems during a crisis, that distinction is critical. When a cyber attack occurs, the priority isn’t just understanding what happened - it’s getting back online, fast.
Sentinel ensures you can.

26 Mar 2026

